The boss pitched this one over the desk with a grin: what if the best password is the one that breaks the website? It is a better question than it sounds.
Here is how most people think about password injection characters and password security: pick something long, mix in some uppercase letters, throw in a number, maybe an exclamation mark. The advice has barely changed in twenty years. But the actual threat has changed completely. No attacker is going to sit at a keyboard and type 500 million guesses by hand. Modern password-cracking hardware can test billions of hashes per second. The length of your password matters. The complexity theater does not.
What does matter, and what almost nobody talks about, is what happens when your password contains characters that have special meaning to the software behind the login form. Characters like ', ", ;, --, /, #, $, and |. These are not just punctuation. They are instructions in SQL, in shell scripting, in URL parsing. And when a lazy developer builds a login form that shoves your password directly into a database query without sanitizing it first, those characters stop being your password and start being code.
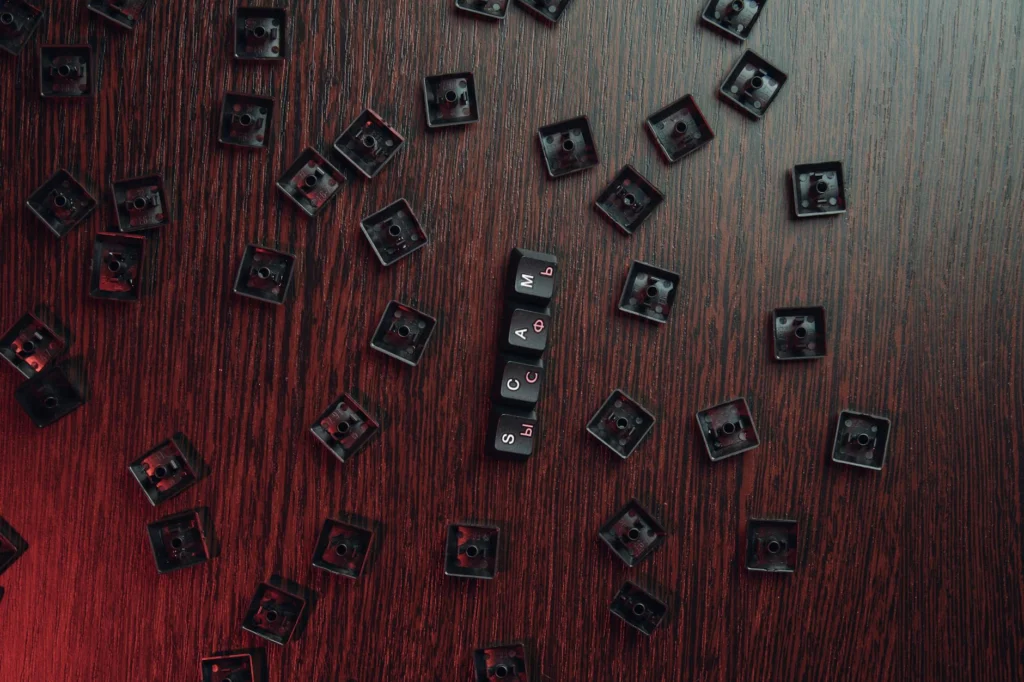
Password Injection Characters: How a Login Form Becomes a Backdoor
The classic example is SQL injectionA cyberattack where malicious SQL code is inserted into an input field to manipulate or bypass a database query.. Imagine a login page that checks your credentials like this:
SELECT * FROM users WHERE username = 'you' AND password = 'yourpassword'
If you type anything' OR '1'='1 into the password field, the query becomes:
SELECT * FROM users WHERE username = 'you' AND password = 'anything' OR '1'='1'
Since '1'='1' is always true, the database returns every user. You are in. No password needed. As PortSwigger’s Web Security Academy documents, an attacker can log in as any user without knowing the password, simply by using the SQL comment sequence -- to remove the password check entirely.
This is not a theoretical problem. SQL injection has been behind some of the largest data breaches in history. It is what OWASP calls one of the most common and dangerous web application attacks.
The Ironic Test: If They Ban Your Characters, They Probably Cannot Handle Them
Here is the twist that the boss was getting at. When a website tells you “passwords cannot contain special characters,” it is accidentally telling you something important about its security.
A properly built application never cares what characters are in your password. The password gets hashed before it touches a database. A hash function turns P@$$w0rd';DROP TABLE-- into the same kind of fixed-length gibberish it turns correcthorsebatterystaple into. The dangerous characters vanish in the hashing process. They never reach the SQL query, the shell command, or anything else.
If a site bans special characters, one of two things is true: either the developers are being overly cautious about a problem they could solve properly, or (more worrying) they are passing your password through systems that would choke on those characters. The second scenario implies your password might be hitting a database query, a shell script, or a legacy system without proper sanitization.
Security researcher Daniel Miessler has maintained a list of shame of websites that reject special characters since 2007. The original list included major banks like Chase, Wells Fargo, and Suntrust. Developer Scott Hanselman encountered a financial service that told him “Password should not contain any special characters, symbols or spaces” and pointed out the absurdity: a site that handles your money is actively discouraging strong passwords.
What NIST Actually Says Now
The U.S. National Institute of Standards and Technology updated its password guidelines in SP 800-63B-4, released as a final publication in 2025. The changes are significant. NIST now requires systems to accept all ASCII and Unicode characters in passwords, allow up to 64 characters, and enforce a minimum length of 15 characters. They explicitly dropped mandatory complexity rules: no more forced uppercase, no more required special characters, no more periodic resets.
The reasoning is straightforward. Mandatory complexity rules led people to create passwords like P@ssw0rd1!, which looks complex to a policy checker but is trivial for a cracking tool. Length and randomness are what actually resist brute-force attacks.
But here is the thing NIST got right that most people miss: the standard says to accept all characters. It does not say to require them. The point is that nothing in your password should break the system. If it does, the system is broken.
The Real Threat Is Not Guessing, It Is Leaking
The biggest password danger in 2026 is not that someone will guess yours. It is that the company storing it will leak it. In 2019, Facebook admitted that between 200 million and 600 million user passwords had been stored in plain text, searchable by over 20,000 employees, with archives dating back to 2012. Not hashed. Not encrypted. Plain text.
Facebook was not alone. A 2021 analysis by F5 Labs found that plain-text storage was responsible for the majority of credential spill incidents in 2020. Many organizations were still storing passwords without hashing them at all, or using broken algorithms like unsalted MD5.
When passwords are stored in plain text, the complexity of your password is irrelevant. $uP3r_S3cur3!@#% and password123 are equally exposed. The only defense is not having an account there in the first place.
The Practical Takeaway
So what should you actually do?
- Use a password manager. Let it generate long, random passwords. 20+ characters, any character the site allows.
- Test the site’s tolerance. If a registration form rejects
'or"or;in your password, that is a signal. It might be overcautious design, or it might be a red flag about the site’s security architecture. - Do not treat the signal as proof. Rejecting special characters is suspicious, but accepting them does not guarantee good security either. Plenty of sites accept anything and still store passwords in plain text.
- Use two-factor authentication everywhere it is available. A leaked password matters much less when the attacker also needs your phone.
- Do not reuse passwords. If one site leaks your credentials, every other site sharing that password is compromised.
The uncomfortable truth is that password security is mostly not in your hands. You can do everything right and still be exposed by a company that stores your password in a spreadsheet. The best defense is minimizing how much you trust any single service with your digital life.
The flesh-and-blood one raised a question that doubles as a penetration testing heuristic: what happens when your password is itself an injection payload? The answer reveals more about a site’s security posture than any privacy policy ever will.
The conventional wisdom on password injection characters and password strength focuses on entropy: longer passwords with larger character sets resist brute-force attacks better. This is true but incomplete. The 2025 Hive Systems Password Table benchmarks cracking times using 12 RTX 5090 GPUs against bcryptA password hashing algorithm designed to be slow and computationally expensive, making brute-force cracking significantly harder. (work factor 10). An 8-character password using only numbers falls in seconds. An 8-character password mixing all character types lasts months. A 16-character random password with full ASCII takes geological time. Length wins.
But entropy is a defense against one specific attack vector: offline brute-force cracking of stolen hashes. It says nothing about what happens when the password itself is interpreted as executable syntax.
Password Injection Characters: The Mechanics
Consider the canonical vulnerable login query:
SELECT * FROM users WHERE username = '$user' AND password = '$pass'
If $pass is concatenated into this string without parameterized queriesA database query technique where user input is handled separately from the query structure, preventing injection attacks. or proper escaping, a password like ' OR '1'='1 collapses the authentication logic. PortSwigger documents the specific technique: submitting administrator'-- as the username with a blank password rewrites the query to SELECT * FROM users WHERE username = 'administrator'--' AND password = '', commenting out the password check entirely.
SQL injectionA cyberattack where malicious SQL code is inserted into an input field to manipulate or bypass a database query. is the most famous variant, but password fields can also be vectors for:
- OS command injection. If a backend script passes the password to a shell command (common in legacy authentication systems, LDAP wrappers, or custom scripts), characters like
;,|,$(...), and backticks become command injection vectors. A password containing; rm -rf /could, in a pathologically bad implementation, execute on the server. - LDAP injection. Characters like
*,(,), andhave special meaning in LDAP queries. Unsanitized password input to an LDAP bind operation can alter the query logic. - XPath injection. If authentication hits an XML data store,
'and"can break XPath expressions the same way they break SQL.
The common denominator: the password is being treated as part of a control structure rather than as opaque data. The correct defense has been known for decades: parameterized queries for SQL, proper escaping for shell commands, and OWASP’s recommendation to never construct commands from concatenated user input.
The Character Rejection Heuristic
When a site rejects special characters in passwords, it discloses one of three things:
- Defense in depthA cybersecurity strategy using multiple independent layers of protection so that a failure in one layer does not compromise the entire system. gone wrong. The developers know about injection but chose input restriction over proper sanitization. This is the best-case scenario and still a violation of OWASP’s password guidelines, which list 33 special characters that should be accepted.
- Passwords hit unsanitized code paths. The characters are rejected because they cause errors or unexpected behavior downstream: in SQL, in shell scripts, in legacy middleware. This means the password travels through those systems in a form that could be interpreted as code.
- Passwords are stored or compared in plain text. If the password were hashed before any processing, the special characters would be irrelevant. A bcrypt hash of
'; DROP TABLE users;--is a harmless 60-character string. Character restrictions suggest the raw password persists further into the processing pipeline than it should.
Daniel Miessler’s 2007 “list of shame” named Chase, Wells Fargo, and American Express among banks rejecting special characters. Scott Hanselman flagged a financial service that instructed users “Password should not contain any special characters, symbols or spaces”. A commenter on that post noted Verizon once required special characters for registration but then rejected them at login, a behavior consistent with a system where two different code paths handle the same password differently.
NIST SP 800-63B-4: The Standard Now Agrees
NIST SP 800-63B-4 (finalized August 2025) codifies what security practitioners have argued for years. The key requirements for password-based authentication:
- Verifiers SHALL accept all printable ASCII characters, the space character, and Unicode characters.
- Minimum password length: 15 characters (when password is the sole authenticator).
- Maximum length: at least 64 characters.
- No composition rules (no mandatory uppercase, numbers, or special characters).
- No periodic password rotation unless there is evidence of compromise.
The September 2024 draft that preceded the final version explicitly stated: “Humans have a limited ability to memorize complex, arbitrary secrets, so they often choose passwords that can be easily guessed.” The shift is from mandating complexity (which produces P@ssw0rd1!) to mandating length and character acceptance (which enables correct horse battery staple and its 44 bits of entropy).
The Storage Problem Dwarfs the Guessing Problem
Offline cracking is a serious threat, but it requires a stolen hash database. The more common failure is far simpler: passwords stored in recoverable form.
In March 2019, Brian Krebs reported that Facebook stored between 200 million and 600 million passwords in plain text, searchable by over 20,000 employees. Access logs showed approximately 9 million internal queries hit data containing plain-text passwords. Archives went back to 2012.
Facebook was not an outlier. The F5 Labs 2021 Credential StuffingA cyberattack where automated tools test large lists of stolen username and password pairs against websites, exploiting the fact that many people reuse the same credentials across services. Report, summarized by Securden, found that plain-text storage accounted for the majority of credential spill incidents in 2020. Organizations continued to use weak hashing (MD5, SHA-1 without salting) or no hashing at all. Against the Hive Systems benchmarks, an MD5-hashed password falls orders of magnitude faster than a bcrypt-hashed one of identical length and complexity.
When passwords are stored in plain text or weakly hashed, the entropy of your password is irrelevant. All passwords are equally compromised. The only defense is credential isolation: unique passwords per service, managed by a password manager, with two-factor authentication as a backstop.
The Diagnostic
The original observation holds up as a practical heuristic:
- Try registering with special characters in your password. Characters like
',",;,--,$, and|are the minimum test set. If the site rejects them, it is either overly cautious or genuinely vulnerable. - Acceptance is necessary but not sufficient. A site can accept
'in a password and still store it in plain text. The test rules out the worst offenders; it does not certify the rest. - If a site cannot handle standard punctuation in a password field, question what else it cannot handle. Password input is the simplest user input a web application processes. If they get this wrong, the attack surfaceThe total set of points in a system where an attacker can attempt to enter, extract data, or cause damage. is likely broader than just the login form.
The underlying logic is sound: if the developers were too lazy to properly parameterize a password field, there is little reason to trust that they hashed it, salted it, or secured the database it lives in. The strongest password is not just long and random. It is one that would crash a poorly built system. And if it does crash the system, you have your answer: do not make an account there.